Apple has a longstanding and largely unspoken policy when it comes to security updates: if your device can run the latest iOS, the pressure to get there is real. Security fixes flow to the newest version first, sometimes exclusively, and users who dig in their heels on older software are left with varying degrees of exposure depending on how serious the threat is. It is not coercion exactly, but the incentive structure is clear enough. Update, or accept the risk.
That policy just cracked.
On April 1, 2026, Apple quietly expanded the availability of iOS 18.7.7 to a much broader range of devices, explicitly to protect users who had chosen not to upgrade to iOS 26. The reason: DarkSword, a sophisticated exploit kit that security researchers at Lookout, iVerify, and Google Threat Intelligence Group had been tracking since late 2025, and which had become too widespread and too dangerous to leave unaddressed. For a company that treats software version fragmentation as a soft enemy, pushing a security update to users who are actively resisting its flagship operating system is a meaningful departure. It deserves more than a changelog entry.
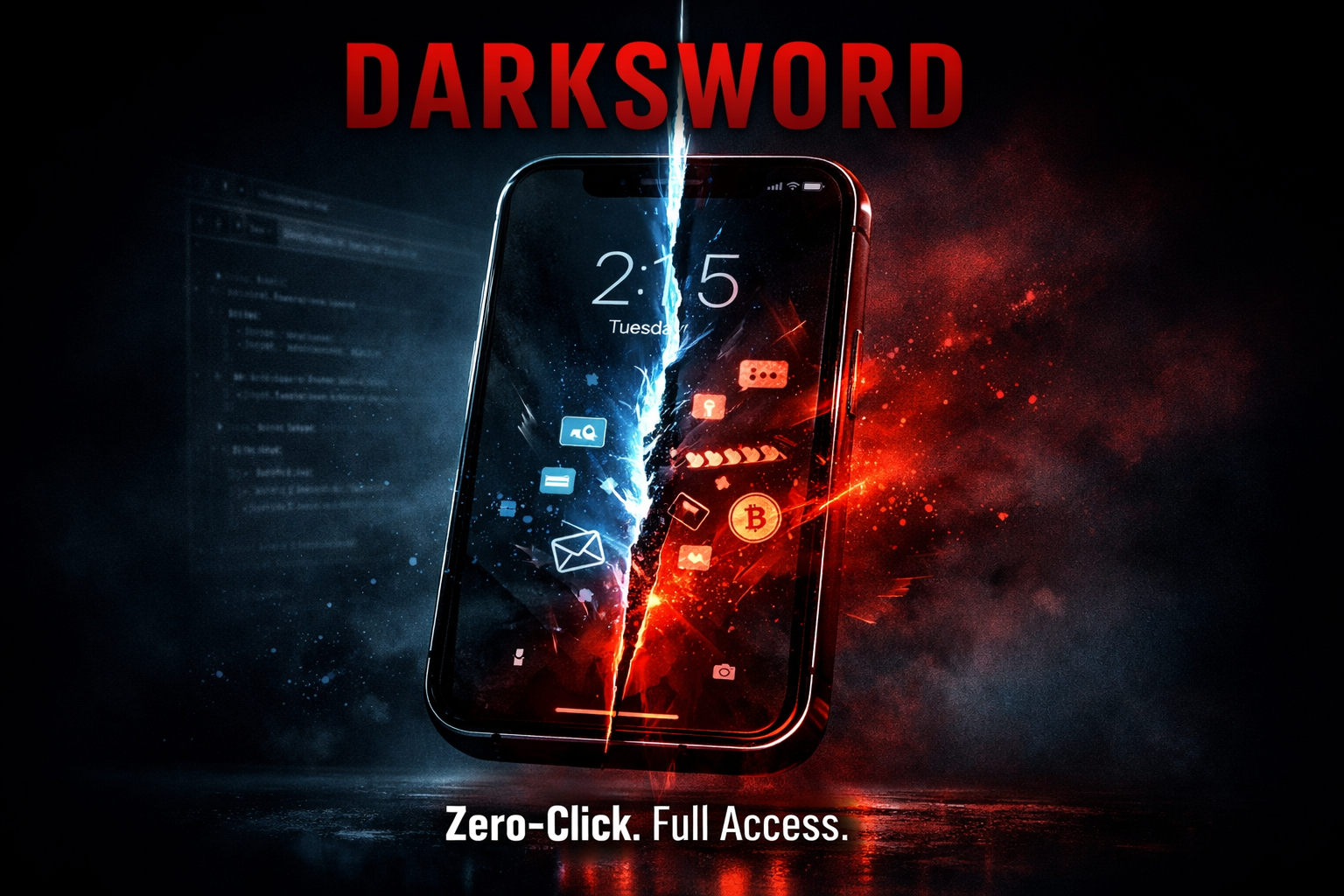
What DarkSword Actually Does
Before getting to Apple's policy shift, it is worth understanding what forced the issue.
DarkSword is a full-chain iOS exploit kit that targets devices running iOS 18.4 through 18.7. It chains six separate vulnerabilities, three of which were exploited as zero-days before Apple had patches in place: CVE-2025-43529 and CVE-2025-43529 (memory corruption in JavaScriptCore), CVE-2025-14174 (a flaw in ANGLE, the graphics library), CVE-2025-43510 and CVE-2025-43520 (kernel vulnerabilities in XNU), and CVE-2026-20700 (a Pointer Authentication Code bypass in dyld). The chain is elegant in a deeply uncomfortable way. It begins in Safari's renderer process, escapes to the GPU sandbox, pivots again into a system service called mediaplaybackd, and from there achieves broad device access.
The kicker is what that access looks like. A successful DarkSword compromise can expose messages, stored passwords, crypto wallet data, Wi-Fi credentials, location history, health data, calendar databases, Safari browsing history, iCloud Drive contents, and app data from Telegram and WhatsApp. All of it, silently, because a user loaded a compromised website. No suspicious link to click. No social engineering. Just a page that fingerprints the device and routes it to the exploit chain if it qualifies.
This is not targeted spyware used against dissidents and journalists in a handful of countries, though it has been used for that too. Security researchers documented use by PARS Defense, a Turkish commercial surveillance vendor, and two separate threat actors tracked as UNC6748 and UNC6353. That last group is a suspected Russian espionage operation that had already incorporated the earlier Coruna exploit kit and pivoted to DarkSword for campaigns targeting Ukrainian users. What made this situation escalate further is that DarkSword's source code was published on GitHub last month, taking it from a tool used by sophisticated state actors and surveillance vendors and putting it within reach of anyone motivated enough to use it.
Apple's Historical Calculus
To understand why iOS 18.7.7 being broadly available matters, you have to understand what Apple normally does. When iOS 26 launched, Apple had already shipped the DarkSword patches in that operating system. Users who upgraded were protected. For devices capable of running iOS 26, Apple's typical approach would be to let the pressure of remaining vulnerable serve as a nudge toward upgrading. Security updates as a carrot, or depending on your perspective, withheld security as a stick.
This time, a significant share of users pushed back. iOS 26 introduced what Apple calls the "Liquid Glass" interface, a design departure that generated enough user friction that a meaningful segment of device owners has simply declined to upgrade. Apple's own data from February 2026 showed that roughly 74% of iPhones introduced in the last four years were running iOS 26. That sounds good until you consider what it leaves behind: approximately 20% of active iOS devices still on iOS 18, which security firms estimated as somewhere between 200 million and 270 million vulnerable handsets. That is not a rounding error. That is a mass exposure event with a publicly available exploit kit and multiple active threat actor campaigns.
The initial iOS 18.7.7 release had been limited to the iPhone XS, XS Max, and XR, the older devices incapable of running iOS 26 at all. Backporting patches to hardware that has no upgrade path is standard Apple practice. What is not standard is what happened next: expanding that same update to every compatible iOS 18 device, including models fully capable of running iOS 26, because millions of users who could upgrade had chosen not to.
When Policy Meets Reality
Apple's security communications around this update were notably direct. The company told users that visiting a compromised website on an older iOS version could result in stolen data, and it warned that this threat is active. iVerify's Rocky Cole put it plainly: "Leaving those users exposed would be a hard decision to defend, particularly for an organization that centers its brand around security and privacy."
That brand calculus matters. Apple's market position is built substantially on the premise that iPhones are more secure than the alternative. DarkSword, left unaddressed for the roughly 20% of iOS users still on iOS 18, would have made that premise harder to defend. It is easy to say "we gave them the option to update" when the threat is low-grade. It is much harder when a publicly leaked exploit kit is being deployed by Russian espionage groups and financially motivated actors, CISA has the associated CVEs in its Known Exploited Vulnerabilities catalog, and the scale of exposure is measured in hundreds of millions of devices.
From an enterprise perspective, this also matters for IT teams who are managing mixed fleets. Device upgrade cycles in organizations do not always align with operating system release schedules. MDM policies can push updates, but there are often exceptions, pilot rings, and compatibility holds that leave a percentage of managed devices on prior versions at any given time. The fact that iOS 18.7.7 now delivers DarkSword protection without forcing a full iOS 26 migration gives administrators meaningful breathing room, even if Apple's strong recommendation remains to get to iOS 26 as quickly as operationally possible.
What This Might Signal
One update does not a policy make. Apple is not announcing that it will routinely backport security fixes to previous major versions while users avoid aesthetic upgrades. The statement in the iOS 18.7.7 changelog is careful: the company "continues to strongly recommend" iOS 26 for the fullest security protections.
But DarkSword has introduced a data point that Apple will have to reckon with going forward. User resistance to major OS redesigns is not a new phenomenon. iOS 7's flat redesign generated backlash. iOS 26's Liquid Glass is generating its own. If a future major version triggers another significant holdout population, and a serious threat emerges that targets those users specifically, Apple's decision here establishes a precedent. The company can backport to the prior major version when the threat is serious enough and the user population is large enough to make withholding patches a reputational and ethical problem.
The more uncomfortable read is that DarkSword revealed something about the limits of Apple's update incentive model. The carrot of features and the stick of unpatched vulnerabilities only work when users are willing to accept the trade-off. When a large enough number of people refuse to upgrade because they dislike the new interface, and a serious enough exploit targets exactly that population, Apple's leverage inverts. The company needed users to be safe more than users needed the latest design language. That is an uncomfortable position for a company that has historically been able to set the terms of its own upgrade cycle.
For iOS 18 users still sitting on the update prompt: install iOS 18.7.7 now if you are not moving to iOS 26. The exploit is real, the kit is public, and drive-by web attacks do not require you to do anything wrong. For everyone else, this episode is a reminder that "up to date" is not just a feature preference. Sometimes it is the only thing standing between your device and someone else's access to everything on it.
Subscribe to our newsletter to get the latest Apple updates and news










Member discussion