Apple quietly shipped something notable yesterday. Not a headline-grabbing OS release, not a new feature — just a small security fix delivered in the background, without asking you to restart your phone. Four versions, all landing simultaneously: iOS 26.3.1 (a), iPadOS 26.3.1 (a), macOS 26.3.1 (a), and macOS 26.3.2 (a). The latter exists because the MacBook Neo shipped with a slightly newer revision of macOS Tahoe than the rest of the Mac lineup.
What makes this moment worth paying attention to isn't the patch itself, though the vulnerability it fixed is real. It's that this is the first time Apple has used its Background Security Improvement infrastructure for a public release — a capability the company has been quietly testing with beta users since January.
What Got Patched, and Why It's Not Trivial
The fix targets WebKit, Apple's browser rendering engine that underpins Safari on every Apple platform. The vulnerability allowed maliciously crafted web content to bypass the Same Origin Policy — a foundational web security boundary that prevents content from one site from accessing data belonging to another. The specific mechanism was a cross-origin issue in the Navigation API, which Apple addressed through improved input validation.
Same Origin Policy bypasses tend to get underplayed in security coverage because they sound abstract. They're not. In practice, a successful exploit could let a malicious site read cookies, session tokens, or other sensitive data from a legitimate site open in the same browser — potentially including banking sessions, email, or enterprise web applications. It doesn't require installing anything. Just visiting the wrong page is enough.
Whether this was being actively exploited in the wild, Apple hasn't said. But the fact that it warranted a dedicated security response outside the normal update cadence suggests the company wasn't inclined to wait.
The Bigger Story: A New Way Apple Pushes Security Fixes
The Background Security Improvement system is designed precisely for moments like this one. Rather than bundling WebKit patches into a full OS update — which requires user action, a restart, and often sits uninstalled on devices for days or weeks — Apple can now deliver targeted fixes to the browser engine and specific system libraries silently, in the background, without disrupting the user at all.
Apple has described the capability as a mechanism to handle components like the Safari browser, WebKit framework stack, and other system libraries that benefit from smaller, ongoing security patches between software updates. Before yesterday, Apple had shipped test versions of the system to beta users starting in January to validate the delivery pipeline. Yesterday was the first time it deployed against a real vulnerability for the public.
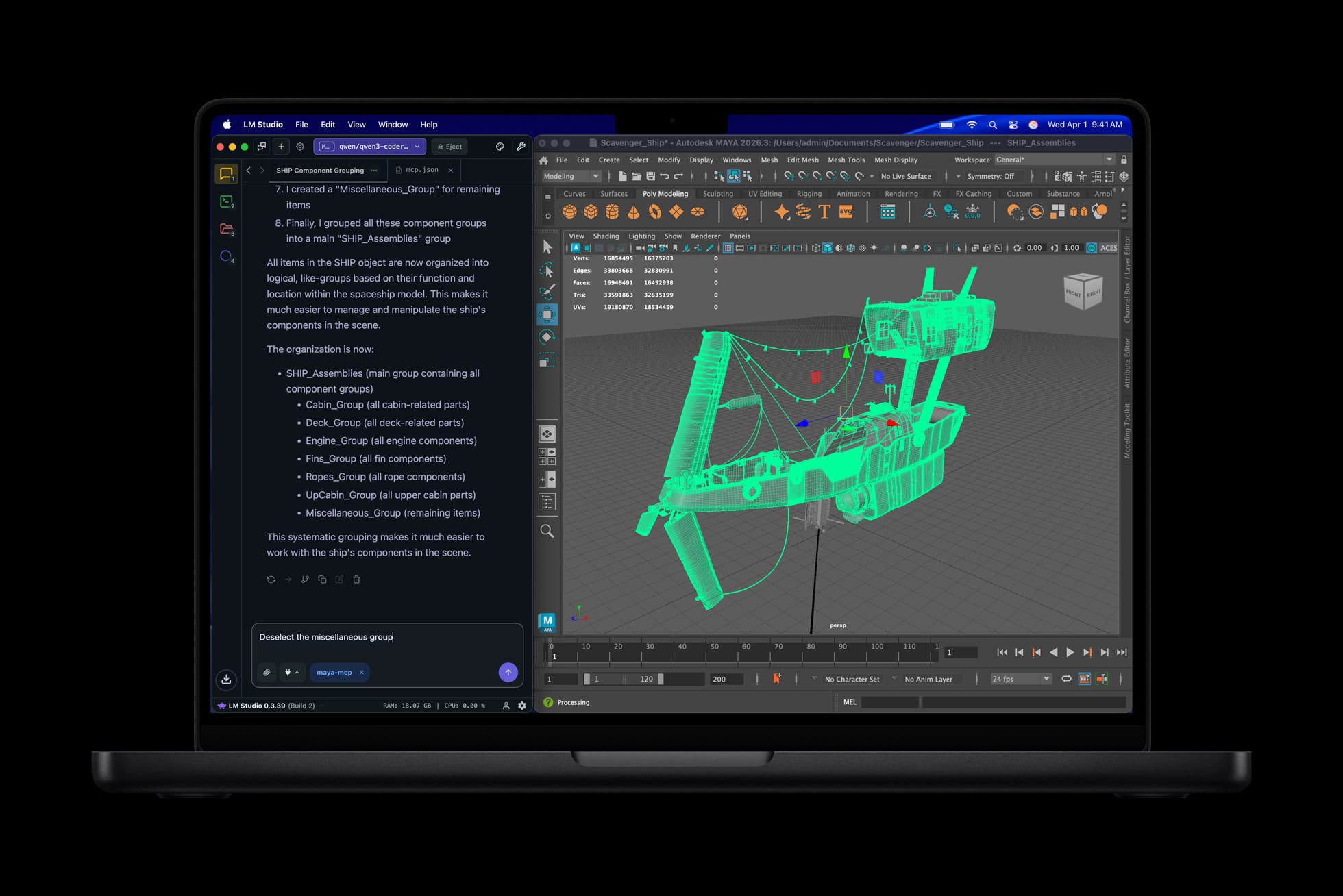
The analogy isn't to Chrome's silent update model exactly — Chrome updates the whole browser, while Apple's system is scoped specifically to components that sit below the full OS update layer. Think of it less like a browser update and more like a targeted hotfix capability that bypasses the traditional software update queue.
For enterprise IT teams, this distinction matters. Background Security Improvements deliver silently and don't require end-user interaction or MDM-initiated prompts. If you're managing a fleet of iPhones or Macs through Intune or Jamf, this means certain WebKit-level patches can land without your orchestration — which is largely a good thing for security posture, but worth understanding as you think about compliance reporting and audit trails.
Why Apple Built This, and What It Says About the Current Threat Landscape
WebKit vulnerabilities have historically been among the most actively exploited in Apple's ecosystem. The browser surface is large, it processes untrusted content by design, and exploitation often requires nothing more than a user visiting a compromised or malicious page. Apple has issued emergency patches for WebKit flaws multiple times in recent years — fixes that required a full OS update that then had to propagate to millions of devices over days.
The Background Security Improvement architecture is Apple's structural answer to that problem. Smaller blast radius, faster delivery, no user friction. The tradeoff is transparency: the update happens without explicit user awareness, which some security-conscious users and IT teams may find uncomfortable. Apple has surfaced these improvements in Privacy & Security settings on both iPhone and Mac, giving users a way to check what's been applied — but most won't look.
Whether that transparency gap becomes a source of concern will depend on how aggressively Apple uses the system going forward. A few WebKit patches a year feels appropriate. Weekly silent updates to an expanding list of components starts to look different.
Yesterday's release was narrow, targeted, and appropriate. It fixed a real vulnerability in the component most exposed to the open web, delivered it to every compatible device silently, and did so without requiring anything from the user. That's the system working exactly as Apple designed it. The question worth watching isn't whether this first deployment was justified — it clearly was. It's what the infrastructure will be used for as Apple grows more comfortable exercising it.








Discussion